Hudson Rock Identifies Real-World Infostealer Infection Targeting OpenClaw Configurations
 Summary
Summary
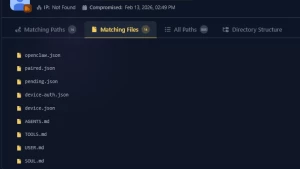
Hudson Rock has identified a real-world infection where an infostealer successfully exfiltrated a victim's OpenClaw configuration environment, marking a shift toward stealing personal AI agent data rather than just browser credentials. The attack was opportunistic; the malware used a general file-grabbing routine targeting sensitive extensions, inadvertently capturing the entire operational context of the AI assistant. The stolen data included the `openclaw.json` file containing an email and a high-entropy Gateway Token, the `device.json` file holding the user's private key (privateKeyPem) which allows attackers to sign messages, and the `soul.md` file detailing the AI's context and access permissions. Hudson Rock warns that as AI agents become integrated into workflows, malware developers will create specialized modules to target this data, as stealing these files grants an attacker a mirror of the victim's life, cryptographic keys, and session tokens for advanced AI models.
(Source:InfoStealers)